1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
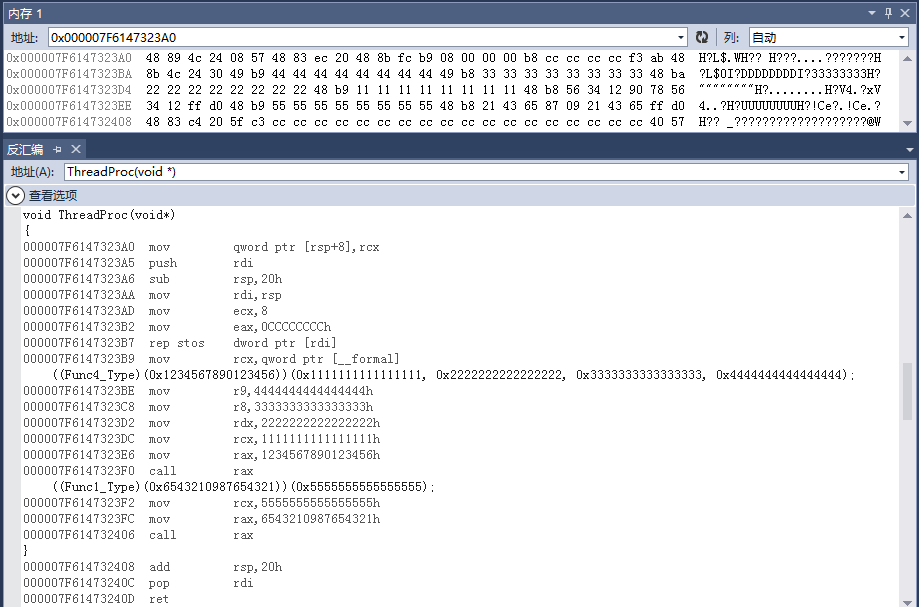
| #include <memory>
#include <string>
#include <Windows.h>
#include "wow64ext.h"
enum class InjectResult {
OK,
Error_OpenProcess,
Error_VirtualAllocEx,
Error_GetProcAddress,
Error_WriteProcessMemory,
Error_CreateRemoteThread
};
template<typename Res, typename Deleter>
class ScopeResource {
Res res;
Deleter deleter;
ScopeResource(const ScopeResource&) {}
public:
Res get() const {
return this->res;
}
ScopeResource(Res res, Deleter deleter) : res(res), deleter(deleter) {}
~ScopeResource() {
this->deleter(this->res);
}
};
InjectResult Wow64InjectWin64(DWORD dwProcessId, const std::wstring& filename)
{
DWORD dwDesiredAccess = PROCESS_CREATE_THREAD | PROCESS_QUERY_INFORMATION | PROCESS_VM_OPERATION | PROCESS_VM_WRITE | PROCESS_VM_READ;
auto closeProcessHandle = [](HANDLE hProcess) {
if(hProcess != NULL) CloseHandle(hProcess);
};
ScopeResource<HANDLE, decltype(closeProcessHandle)> targetProcessHandle(OpenProcess(dwDesiredAccess, FALSE, dwProcessId), closeProcessHandle);
if(targetProcessHandle.get() == NULL) {
return InjectResult::Error_OpenProcess;
}
unsigned char injectCode[] = {
0x48, 0x89, 0x4c, 0x24, 0x08,
0x57,
0x48, 0x83, 0xec, 0x20,
0x48, 0x8b, 0xfc,
0xb9, 0x08, 0x00, 0x00, 0x00,
0xb8, 0xcc, 0xcc, 0xcc, 0xcc,
0xf3, 0xab,
0x48, 0x8b, 0x4c, 0x24, 0x30,
0x49, 0xb9, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x49, 0xb8, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x48, 0xba, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x48, 0xb9, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x48, 0xb8, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0xff, 0xd0,
0x48, 0xb9, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x48, 0xb8, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0xff, 0xd0
};
size_t parametersMemSize = sizeof(DWORD64) + sizeof(_UNICODE_STRING_T<DWORD64>) + (filename.size() + 1) * sizeof(wchar_t);
auto freeInjectCodeMem = [&targetProcessHandle, &injectCode](DWORD64 address) {
if(address != 0) VirtualFreeEx64(targetProcessHandle.get(), address, sizeof(injectCode), MEM_COMMIT | MEM_RESERVE);
};
ScopeResource<DWORD64, decltype(freeInjectCodeMem)> injectCodeMem(VirtualAllocEx64(targetProcessHandle.get(), NULL, sizeof(injectCode), MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE), freeInjectCodeMem);
auto freeParametersMem = [&targetProcessHandle, parametersMemSize](DWORD64 address) {
if(address != 0) VirtualFreeEx64(targetProcessHandle.get(), address, parametersMemSize, MEM_COMMIT | MEM_RESERVE);
};
ScopeResource<DWORD64, decltype(freeParametersMem)> parametersMem(VirtualAllocEx64(targetProcessHandle.get(), NULL, parametersMemSize, MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE), freeParametersMem);
if (injectCodeMem.get() == 0 || parametersMem.get() == 0) {
return InjectResult::Error_VirtualAllocEx;
}
DWORD64 ntdll64 = GetModuleHandle64(L"ntdll.dll");
DWORD64 ntdll_LdrLoadDll = GetProcAddress64(ntdll64, "LdrLoadDll");
DWORD64 ntdll_RtlExitUserThread = GetProcAddress64(ntdll64, "RtlExitUserThread");
DWORD64 ntdll_RtlCreateUserThread = GetProcAddress64(ntdll64, "RtlCreateUserThread");
if(ntdll_LdrLoadDll == 0 || ntdll_RtlExitUserThread == 0 || ntdll_RtlCreateUserThread == 0) {
return InjectResult::Error_GetProcAddress;
}
std::unique_ptr<unsigned char[]> parameters(new unsigned char[parametersMemSize]);
std::memset(parameters.get(), 0, parametersMemSize);
_UNICODE_STRING_T<DWORD64>* upath = reinterpret_cast<_UNICODE_STRING_T<DWORD64>*>(parameters.get() + sizeof(DWORD64));
upath->Length = filename.size() * sizeof(wchar_t);
upath->MaximumLength = (filename.size() + 1) * sizeof(wchar_t);
wchar_t* path = reinterpret_cast<wchar_t*>(parameters.get() + sizeof(DWORD64) + sizeof(_UNICODE_STRING_T<DWORD64>));
std::copy(filename.begin(), filename.end(), path);
upath->Buffer = parametersMem.get() + sizeof(DWORD64) + sizeof(_UNICODE_STRING_T<DWORD64>);
union {
DWORD64 from;
unsigned char to[8];
} cvt;
cvt.from = parametersMem.get();
std::memcpy(injectCode + 32, cvt.to, sizeof(cvt.to));
cvt.from = parametersMem.get() + sizeof(DWORD64);
std::memcpy(injectCode + 42, cvt.to, sizeof(cvt.to));
cvt.from = ntdll_LdrLoadDll;
std::memcpy(injectCode + 72, cvt.to, sizeof(cvt.to));
cvt.from = ntdll_RtlExitUserThread;
std::memcpy(injectCode + 94, cvt.to, sizeof(cvt.to));
if(FALSE == WriteProcessMemory64(targetProcessHandle.get(), injectCodeMem.get(), injectCode, sizeof(injectCode), NULL)
|| FALSE == WriteProcessMemory64(targetProcessHandle.get(), parametersMem.get(), parameters.get(), parametersMemSize, NULL)) {
return InjectResult::Error_WriteProcessMemory;
}
DWORD64 hRemoteThread = 0;
struct {
DWORD64 UniqueProcess;
DWORD64 UniqueThread;
} client_id;
X64Call(ntdll_RtlCreateUserThread, 10,
(DWORD64)targetProcessHandle.get(),
(DWORD64)NULL,
(DWORD64)FALSE,
(DWORD64)0,
(DWORD64)NULL,
(DWORD64)NULL,
injectCodeMem.get(),
(DWORD64)NULL,
(DWORD64)&hRemoteThread,
(DWORD64)&client_id);
if(hRemoteThread != 0) {
CloseHandle((HANDLE)hRemoteThread);
return InjectResult::OK;
}
return InjectResult::Error_CreateRemoteThread;
}
|